Spring Boot AI MCP Server Integration with Azure API Management
Learn how to integrate Spring Boot AI MCP servers in Azure Kubernetes Service with API Management when lacking Swagger documentation. Manual configuration guide for secure access.
How can I access a Spring Boot AI MCP server deployed in Azure Kubernetes Service (AKS) through Azure API Management (APIM) when the server lacks REST endpoints for Swagger documentation?
When deploying a Spring Boot AI MCP server in Azure Kubernetes Service and needing to access it through Azure API Management without Swagger documentation, you can manually configure API Management by creating a blank API and setting up routing parameters. This approach bypasses the need for OpenAPI specifications by directly configuring necessary routing parameters between your AKS-deployed Spring Boot service and the API Management gateway, allowing secure access to your MCP endpoints even without standard REST documentation.
Contents
- Understanding the Spring Boot AI MCP Server in Azure Kubernetes Service
- Azure API Management Integration Without Swagger Documentation
- Manual API Configuration in Azure API Management
- Setting Up Routing Parameters for Spring Boot Services
- Configuring Backend Service URLs and Operation Endpoints
- Testing and Validating the API Management Configuration
- Best Practices for Secure Access to Spring Boot AI MCP Servers
Understanding the Spring Boot AI MCP Server in Azure Kubernetes Service
Spring Boot AI MCP servers provide a robust foundation for machine learning model deployment in cloud environments. When deployed to Azure Kubernetes Service (AKS), these servers leverage containerization for scalability and resilience. However, a common challenge arises when these servers lack traditional REST endpoints for Swagger documentation, making integration with API management solutions like Azure API Management (APIM) more complex.
The Spring Boot framework, particularly in version 3.x, offers extensive configuration options for customizing service behavior. In the context of AI MCP servers, this might mean implementing proprietary communication protocols instead of standard REST APIs. While this approach can enhance security and efficiency, it creates integration challenges when attempting to expose these services through API gateways that typically expect OpenAPI/Swagger specifications.
Understanding your Spring Boot AI MCP server’s internal architecture is crucial before proceeding with API Management integration. You’ll need to identify:
- The specific endpoints your MCP server exposes
- The authentication mechanisms it uses
- The request/response formats it expects
- Any custom headers or parameters required for proper operation
This knowledge forms the foundation of your API Management configuration strategy, allowing you to map APIM operations to your actual backend endpoints despite the lack of standard documentation.
Azure API Management Integration Without Swagger Documentation
Azure API Management serves as a comprehensive gateway for managing APIs, offering features like security, throttling, caching, and monitoring. Traditionally, APIM integration relies on OpenAPI specifications (formerly Swagger) to automatically generate API definitions and operations. However, when your Spring Boot AI MCP server lacks these standard REST endpoints, you need an alternative approach.
The solution lies in manually configuring your API Management instance to work with your Spring Boot service. This involves creating a blank API and defining the routing parameters yourself. APIM acts as a proxy, intercepting incoming requests and forwarding them to your backend service based on the configuration you establish.
The routing pattern in this scenario follows: [API Management gateway URL] + [API URL suffix] + [Operation endpoint]. This structure allows APIM to correctly route requests to your AKS-deployed Spring Boot AI MCP server, even without automatic Swagger-based discovery.
Several benefits come with this manual approach:
- Complete control over how your API is exposed
- Ability to implement custom transformations and policies
- Enhanced security through selective endpoint exposure
- Better performance by avoiding unnecessary documentation parsing overhead
While this method requires more manual configuration, it provides the flexibility needed to integrate non-standard Spring Boot services with enterprise API management solutions.
Manual API Configuration in Azure API Management
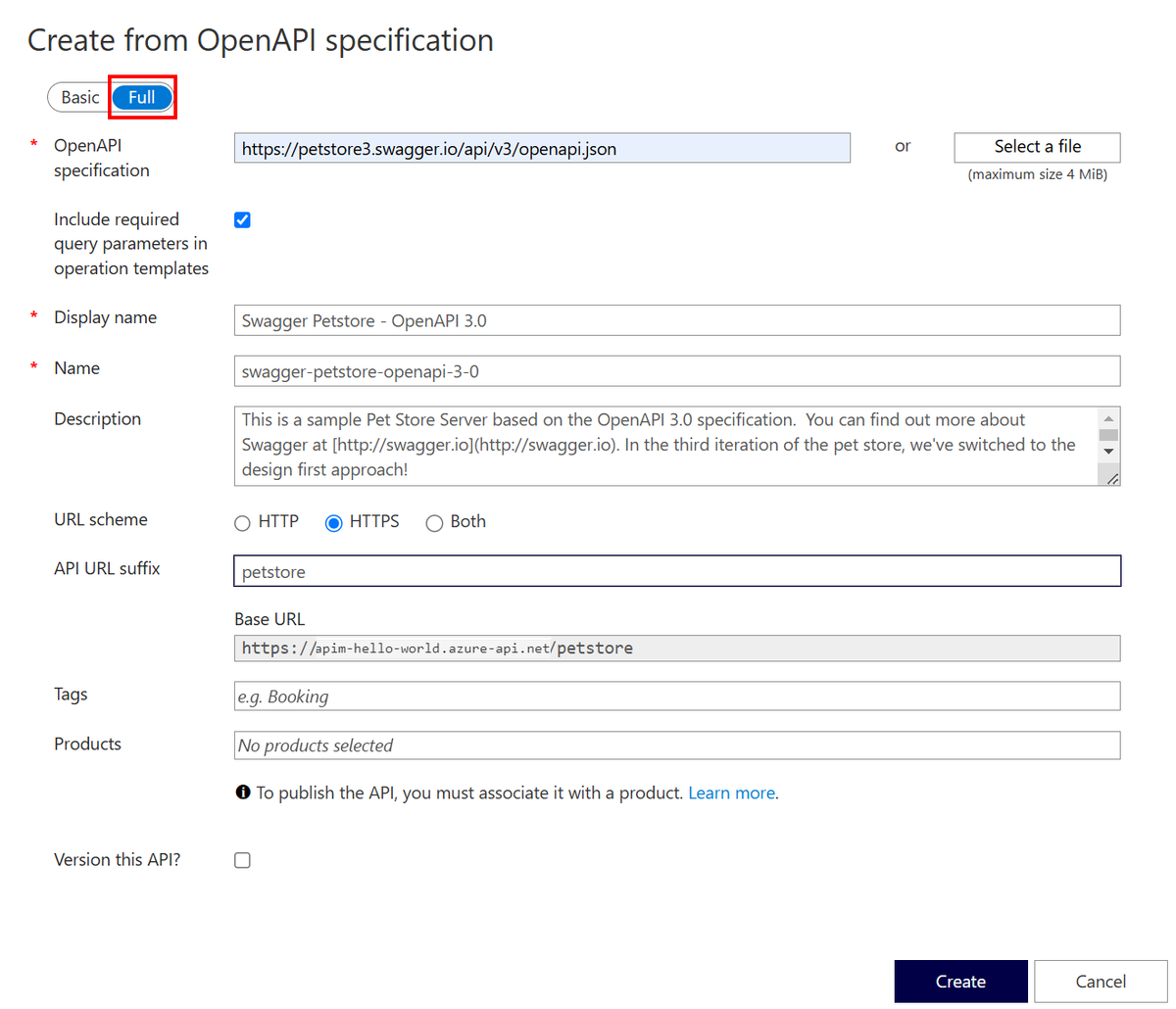
Creating a manual API configuration in Azure API Management is straightforward and begins in the Azure portal. Navigate to your API Management instance and select “APIs” from the left menu, then click “Add API” and choose “Blank API”. This option allows you to define your API structure without relying on an OpenAPI specification.
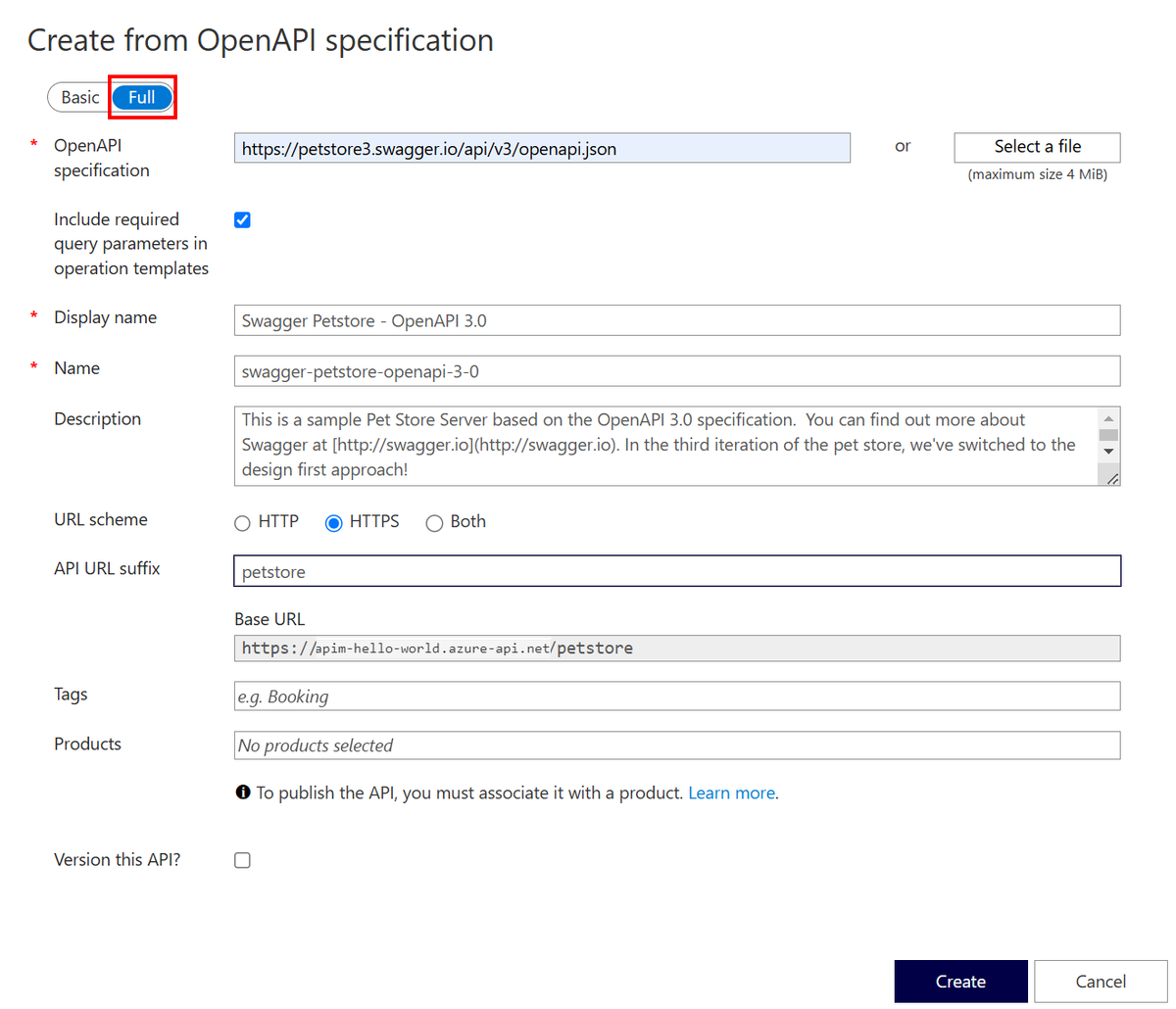
When configuring your blank API, several key parameters require attention:
- API name: Give your API a descriptive name that reflects its purpose
- API URL suffix: This is crucial for routing - use a unique identifier like “mcp” or “ai-server”
- Service URL: Set this to your AKS-deployed Spring Boot service endpoint
- API type: Select “HTTP” unless your service uses a different protocol
The API URL suffix determines how your API will be accessed through the APIM gateway. For a Spring Boot AI MCP server, something like “/mcp” would be appropriate, resulting in a full endpoint path of [APIM gateway URL]/mcp/[operation endpoint].
After creating the API, you’ll need to define the operations manually. Each operation corresponds to an endpoint exposed by your Spring Boot AI MCP server. For each operation, specify:
- HTTP method (GET, POST, PUT, DELETE, etc.)
- Relative URL path (must exactly match your backend endpoint)
- Description and display name for clarity
This manual process ensures that your API Management instance can properly route requests to your Spring Boot service, even without automatic documentation generation. The key is maintaining consistency between the operation paths defined in APIM and the actual endpoints exposed by your backend service.
Setting Up Routing Parameters for Spring Boot Services
Proper routing parameter configuration is essential for successfully connecting Azure API Management to your Spring Boot AI MCP server. The routing pattern consists of three main components that must work together seamlessly:
-
API Management Gateway URL: This is the base URL for your API Management instance, typically in the format https://[your-apim-name].azure-api.net/
-
API URL Suffix: The unique identifier you assigned when creating your API (e.g., “mcp”). This helps organize different APIs within your APIM instance.
-
Operation Endpoint: The specific path that matches your Spring Boot AI MCP server’s endpoint. This must exactly correspond to the path defined in your Spring Boot application.
For example, if your Spring Boot AI MCP server has an endpoint at “/v1/chat/completion”, you would:
- Set the API URL suffix to “mcp”
- Create an operation with the relative URL path “/v1/chat/completion”
- The full request URL through APIM would be: https://[your-apim-name].azure-api.net/mcp/v1/chat/completion
When setting up routing parameters, consider these best practices:
- Use consistent naming conventions across your API Management and Spring Boot service
- Implement versioning in your URL structure (e.g., /v1/, /v2/) to facilitate future updates
- Document your routing scheme for team members who may need to understand the architecture
- Test routing thoroughly with various endpoints to ensure proper request forwarding
Spring Boot configuration plays a significant role in how your endpoints are exposed. Ensure your application.properties or application.yml files correctly define the context path and server port that align with your AKS deployment setup.
Configuring Backend Service URLs and Operation Endpoints
Once you’ve established the basic routing structure, configuring the backend service URLs and operation endpoints requires attention to detail. Navigate to your API in the Azure portal and select “Settings” to access the backend configuration options.
The Web service URL parameter is perhaps the most critical setting in this configuration. This should point directly to your AKS-deployed Spring Boot AI MCP service endpoint. The format typically includes:
- The AKS cluster’s internal or external IP address
- The port your Spring Boot service is listening on
- Any necessary path components
For Spring Boot applications running in AKS, this URL might look something like:
https://[aks-cluster-ip]:[service-port]/[context-path]
When configuring operation endpoints, remember that they must exactly match the paths defined in your Spring Boot AI MCP server. Any discrepancy will result in 404 errors as requests fail to reach the intended backend endpoints.
Additional configuration considerations include:
- Backend timeout settings: Adjust based on your AI model’s processing time
- Protocol: Ensure it matches your Spring Boot service (HTTP or HTTPS)
- Authentication: Configure any required authentication headers or certificates
- SSL verification: Consider whether to validate the SSL certificate of your backend service
Spring Boot’s flexible configuration allows you to customize how these endpoints behave. You might need to adjust properties in your application configuration to ensure compatibility with the API Management gateway:
# Application properties for Spring Boot AI MCP server
server.port=8080
server.ssl.enabled=true
management.endpoints.web.exposure.include=health,info
spring.application.name=ai-mcp-server
These configurations ensure your Spring Boot service operates harmoniously with the API Management layer, providing the necessary endpoints for successful integration.
Testing and Validating the API Management Configuration
After configuring your Azure API Management instance to connect with your Spring Boot AI MCP server, thorough testing is essential to ensure everything functions correctly. The Azure portal provides a built-in test console that allows you to validate your configuration without writing custom code.
To test your API configuration:
- Navigate to your API in the Azure portal
- Select an operation from the list
- Click the “Test” tab
- Provide any required parameters or request body
- Click “Send” to execute the request
The test console will display both the request sent to your backend service and the response received. This helps identify issues such as:
- Incorrect endpoint routing (404 errors)
- Authentication problems (401/403 errors)
- Request format mismatches (400 errors)
- Backend service connectivity issues
When testing Spring Boot AI MCP server integration, pay special attention to:
- Proper request headers, especially authentication tokens
- Correct request body format for your specific AI model
- Response handling and error scenarios
- Performance characteristics under load
Beyond the portal’s test console, consider implementing additional validation approaches:
- Create automated test scripts that exercise various endpoints
- Monitor backend service logs for incoming requests from API Management
- Use network tracing tools to verify request routing
- Implement health check endpoints in your Spring Boot service for monitoring
Spring Boot Actuator provides excellent endpoints for monitoring your application’s health and metrics. Consider exposing these through your API Management instance to gain insights into your backend service’s performance:
# Enable Spring Boot Actuator endpoints
management.endpoints.web.exposure.include=health,info,metrics
management.endpoint.health.show-details=always
By thoroughly testing and validating your configuration, you can ensure reliable operation of your Spring Boot AI MCP server through Azure API Management, even without standard Swagger documentation.
Best Practices for Secure Access to Spring Boot AI MCP Servers
Implementing secure access to your Spring Boot AI MCP servers through Azure API Management requires careful consideration of several factors. Following best practices ensures both security and performance in your integration architecture.
Authentication and Authorization
Implement robust authentication mechanisms at both the API Management and Spring Boot service levels:
- Use APIM policies for authentication before requests reach your backend
- Implement OAuth2, API keys, or JWT validation in your Spring Boot application
- Consider Azure Active Directory integration for enterprise scenarios
Security Headers
Configure appropriate security headers in your Spring Boot application:
@Bean
public SecurityFilterChain securityFilterChain(HttpSecurity http) throws Exception {
http
.headers()
.contentSecurityPolicy("default-src 'self'")
.and()
.xssProtection()
.and()
.frameOptions().sameOrigin()
.and()
.httpStrictTransportSecurity()
.includeSubDomains(true)
.maxAgePreload(31536000)
.preload(true)
.and()
.authorizeHttpRequests()
.requestMatchers("/actuator/**").permitAll()
.anyRequest().authenticated()
.and()
.oauth2ResourceServer()
.jwt();
return http.build();
}
Network Security
- Implement network security groups (NSGs) in AKS to restrict traffic
- Use private endpoints for sensitive services
- Configure SSL/TLS encryption for all communications
- Consider implementing service mesh for advanced traffic management
Monitoring and Logging
- Enable comprehensive logging in both APIM and Spring Boot
- Implement distributed tracing to follow requests across the architecture
- Set up alerts for unusual activity or performance degradation
- Regularly review access patterns and adjust security policies accordingly
Performance Optimization
- Implement caching in APIM for frequently accessed AI model responses
- Configure appropriate timeout values for your AI model processing times
- Consider request batching for operations that support it
- Monitor resource utilization in both AKS and APIM
By following these best practices, you can create a secure, reliable integration between your Azure API Management instance and Spring Boot AI MCP servers, ensuring that your AI services remain accessible and protected even without traditional REST documentation.
Sources
- Microsoft Learn API Management Documentation - Creating APIs from scratch in Azure API Management: https://learn.microsoft.com/en-us/azure/api-management/api-management-howto-create-apis#-create-an-api-from-scratch
- Spring Boot Official Documentation - RESTful Web Services with Spring Boot: https://spring.io/guides/gs/rest-service/
- Azure Kubernetes Service Documentation - Deploying applications to AKS: https://learn.microsoft.com/en-us/azure/aks/kubernetes-walkthrough
- Spring Security Guide - Securing Spring Boot applications: https://spring.io/guides/gs/securing-web/
- API Management Developer Guide - Backend service configuration: https://learn.microsoft.com/en-us/azure/api-management/api-management-howto-configure-backend-service
Conclusion
Integrating a Spring Boot AI MCP server deployed in Azure Kubernetes Service with Azure API Management without Swagger documentation is achievable through manual configuration approaches. By creating a blank API in APIM and carefully setting up routing parameters, backend service URLs, and operation endpoints, you can establish a secure gateway to your AI services.
The key to successful integration lies in understanding the specific requirements of your Spring Boot AI MCP server and meticulously configuring each parameter in API Management to match your backend service’s endpoints. While this approach requires more manual effort than Swagger-based integration, it provides greater control and flexibility for non-standard service architectures.
Following best practices for security, monitoring, and performance optimization ensures your integration remains robust and scalable as your AI service usage grows. With proper configuration and testing, Azure API Management can effectively serve as a gateway to your Spring Boot AI MCP servers, providing enterprise-level management capabilities even without traditional REST documentation.
When your Spring Boot AI MCP server lacks Swagger documentation, manually configure API Management by creating a blank API and setting routing parameters. API Management acts as a gateway using the pattern: [API Management gateway URL] + [API URL suffix] + [Operation endpoint] to route requests to your backend service. Set the Web service URL to your AKS-deployed Spring Boot service endpoint and define a unique API URL suffix (e.g., “mcp”). Manually add operations that match your server’s endpoints, ensuring the Operation endpoint is identical in both API Management and your backend to prevent 404 errors. You can modify API settings through the Settings tab to configure backend service URLs and operation endpoints after creation. Test your configuration using the portal’s test console with appropriate subscription keys. This manual approach bypasses the need for OpenAPI specifications by directly configuring the necessary routing parameters. The routing pattern requires careful configuration of the Web service URL to point to your AKS cluster endpoint.
