Identity Validation in Microservices: Local vs Centralized Approaches
Exploring authentication and authorization approaches in microservices: local validation vs centralized services with hybrid solutions for multi-tenant platforms.
What are the best practices for identity validation in microservices architecture: local validation with short-lived contexts versus centralized validation service? How do hybrid approaches (local validation for most endpoints with centralized validation for high-risk operations) compare in terms of latency, revocation consistency, operational complexity, and failure modes? What real-world experiences and trade-offs should be considered when implementing identity validation in a multi-tenant microservices platform with identity-based access control?
Identity validation in microservices architecture requires careful consideration between local validation with short-lived contexts and centralized validation services, with hybrid approaches offering balanced solutions for multi-tenant platforms. Authentication and authorization decisions significantly impact performance, security, and operational complexity in distributed systems, making the choice between validation approaches critical for system design and user experience.
Contents
- Understanding Identity Validation in Microservices Architecture
- Local Validation with Short-Lived Contexts: Implementation and Benefits
- Centralized Validation Services: Architecture and Advantages
- Hybrid Approaches: Balancing Performance and Security
- Multi-Tenant Identity Management: Challenges and Solutions
- Real-World Trade-offs and Case Studies
- Best Practices for Identity Validation in Microservices
Understanding Identity Validation in Microservices Architecture
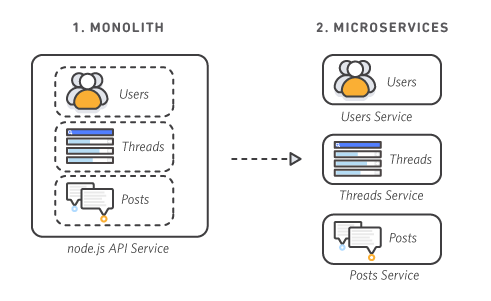
Microservices architecture fundamentally changes how identity validation works in distributed systems. Unlike monolithic applications where authentication typically happens once at the entry point, microservices require a more nuanced approach to identity management. Each service operates independently, communicating through well-defined APIs, which creates both opportunities and challenges for maintaining security while optimizing performance.
The autonomous nature of microservices allows teams to implement different validation strategies based on specific security requirements and performance needs. However, this independence also means that traditional authentication patterns need rethinking. In a microservices environment, identity validation must account for service-to-service communication, horizontal scaling, eventual consistency, and distributed tracing – all while maintaining robust access control mechanisms.
The core challenge lies in balancing security with performance. Every authentication decision introduces latency, and in a distributed system with potentially dozens of services, this can compound significantly. Additionally, token validation must account for revocation scenarios, operational complexity, and the unique demands of multi-tenant platforms where identity-based access control becomes increasingly important.
Local Validation with Short-Lived Contexts: Implementation and Benefits
Local validation with short-lived contexts is a popular approach in microservices architecture where each service validates authentication tokens independently without external dependencies. This method typically involves using JWT (JSON Web Tokens) with short expiration times, allowing services to validate signatures locally while minimizing revocation latency.
The implementation usually follows this pattern: when a user authenticates, they receive a JWT with a short expiration time (typically 5-15 minutes). Each microservice validates the token locally using a shared public key. The service also maintains a local cache of recently invalidated tokens to handle revocation scenarios. This approach dramatically reduces latency because services don’t need to make external calls for token validation.
What makes this approach particularly effective? The elimination of external dependencies means each service can operate autonomously, which aligns perfectly with the core principles of microservices. No single point of failure exists in the authentication system, and services can continue functioning even if the authentication service is temporarily unavailable. This architecture also scales beautifully – as you add more services, authentication load doesn’t increase on any central component.
The short-lived nature of these tokens creates a natural security boundary. If a token is compromised, it becomes useless within minutes rather than hours. This dramatically reduces the window of opportunity for attackers to misuse stolen credentials. Additionally, the local validation approach simplifies operational complexity since each service handles its own authentication logic without needing to coordinate with external services.
But what about the trade-offs? The primary challenge lies in handling token revocation. Since tokens are valid for a limited time, you must maintain a cache of recently invalidated tokens to prevent users from using revoked tokens before they naturally expire. This cache must be consistent across all services, which can become complex in large deployments. There’s also the operational overhead of managing key rotation and ensuring all services have access to the latest public keys.
Centralized Validation Services: Architecture and Advantages
Centralized validation services take a fundamentally different approach by concentrating all authentication logic in a dedicated service. In this architecture, microservices forward authentication requests to a centralized service that validates tokens and returns authorization decisions. This pattern resembles traditional monolithic authentication but adapted for distributed systems.
The implementation typically involves an authentication service that handles all token validation. When a microservice receives a request with an authentication token, it calls the authentication service via an internal API. The authentication service validates the token signature, checks revocation status, evaluates user permissions, and returns an authorization decision. This approach ensures consistent validation logic across all services while providing a single source of truth for authentication state.
What are the key advantages of this approach? First and foremost is perfect consistency in token validation. Since all services validate tokens through the same service, there’s no risk of inconsistent authentication decisions across the system. This is particularly valuable in environments where compliance requires strict audit trails and consistent security policies.
Centralized validation also simplifies revocation handling. When a token needs to be revoked, the authentication service can immediately invalidate it across the entire system. There’s no need to maintain distributed caches of invalidated tokens, which eliminates a significant operational complexity. Additionally, centralized services can implement more sophisticated authentication logic, such as multi-factor authentication checks, behavior analysis, or integration with external identity providers.
But wait – doesn’t this create a single point of failure? Modern implementations address this concern through redundancy and horizontal scaling. The authentication service can be deployed across multiple instances with load balancing, ensuring high availability. Additionally, services can implement circuit breakers to handle temporary unavailability, falling back to cached authentication decisions or rejecting requests when the authentication service is unavailable.
The centralized approach also excels in providing comprehensive audit trails and monitoring. Since all authentication requests flow through a single service, it’s easier to implement detailed logging, metrics collection, and anomaly detection. This visibility is crucial for security teams investigating potential breaches or troubleshooting authentication issues.
However, the centralized approach introduces significant latency. Each authentication request requires an external call, which can dramatically increase response times in systems with many services. In high-throughput scenarios, this latency can become a bottleneck, affecting user experience and system performance. Additionally, the centralized service becomes a critical dependency – if it experiences issues, it can impact the entire system’s availability.
Hybrid Approaches: Balancing Performance and Security
Hybrid approaches represent the sweet spot for many microservices architectures, combining the best elements of local validation and centralized services. In this model, most endpoints use local validation with short-lived contexts for optimal performance, while high-risk operations leverage centralized validation for enhanced security and consistency.
The implementation typically involves a tiered authentication strategy. Standard API endpoints use JWT tokens with short expiration times and local validation, providing fast authentication with minimal latency. For sensitive operations like password changes, financial transactions, or administrative actions, services make external calls to a centralized validation service that performs additional checks, such as verifying the user’s recent activity or requiring multi-factor authentication.
What makes hybrid approaches so effective? They address the fundamental tension between performance and security. By applying different validation strategies based on risk level, you can optimize for speed where it matters most while maintaining robust security where it’s most critical. This targeted approach prevents unnecessary authentication overhead across the entire system while still providing comprehensive protection for sensitive operations.
The hybrid model also offers operational flexibility. Teams can implement different validation policies for different services or even different endpoints within the same service. This granularity allows organizations to align authentication strategies with business requirements, regulatory needs, and risk assessments. For example, a payment service might require centralized validation for transactions while using local validation for basic account lookups.
But how do you handle the complexity of maintaining two different validation systems? The key is abstraction. By creating unified authentication interfaces that handle both local and centralized validation transparently, services can use the same authentication logic regardless of the underlying implementation. This abstraction layer can automatically route requests to the appropriate validation method based on configured policies.
Latency optimization in hybrid approaches requires careful consideration. For local validation, the focus is on minimizing token size and validation overhead. For centralized validation, the emphasis is on minimizing response times through efficient caching, connection pooling, and asynchronous processing. Some implementations use a “hot cache” of recently validated tokens to reduce repeated calls to the centralized service for the same user.
Revocation consistency becomes particularly interesting in hybrid models. The approach typically combines short-lived tokens with immediate invalidation through the centralized service. When a token needs to be revoked, the centralized service immediately invalidates it and notifies all services to clear any cached authentication decisions. This creates a near-real-time revocation system while still benefiting from the performance advantages of local validation.
Failure mode analysis reveals that hybrid approaches offer better fault tolerance than purely centralized systems. If the centralized validation service experiences issues, services can fall back to local validation with appropriate security constraints. This graceful degradation ensures the system remains operational even during authentication service outages, though with potentially reduced security for certain operations.
Multi-Tenant Identity Management: Challenges and Solutions
Multi-tenant microservices platforms introduce unique challenges for identity validation that don’t exist in single-tenant environments. In these systems, multiple customers share the same infrastructure while requiring strict isolation of their identity data and access controls. The validation approach must accommodate tenant-specific authentication policies, data segregation, and compliance requirements.
The core challenge lies in maintaining tenant isolation while providing efficient authentication across the entire platform. When services validate tokens, they need to understand which tenant the user belongs to and apply the appropriate access controls. This requires embedding tenant information in authentication tokens or implementing a tenant-aware validation layer that can route requests to tenant-specific authentication logic.
What makes multi-tenant identity management particularly complex? The need to balance isolation with efficiency. Each tenant might have different authentication policies – some requiring multi-factor authentication, others having specific session timeout requirements, and still others needing integration with their identity providers. The validation system must accommodate these variations without creating performance bottlenecks or operational complexity.
Hybrid approaches often shine in multi-tenant environments. Most operations can use local validation with tenant-specific short-lived tokens, maintaining performance while ensuring isolation. For high-risk operations or when tenant-specific policies require centralized validation, services can make targeted calls to tenant-aware authentication services. This approach provides the flexibility needed to accommodate diverse tenant requirements while keeping the system performant.
Token design becomes crucial in multi-tenant scenarios. Tokens must include sufficient information for services to determine tenant membership and apply appropriate access controls, but they shouldn’t become so large that they impact performance. Common approaches include embedding tenant IDs in token claims, using tenant-specific signing keys, or implementing token validation that includes tenant context.
Operational complexity increases significantly in multi-tenant environments. Teams must manage tenant-specific authentication policies, key rotation for each tenant, and tenant isolation in the authentication service. The challenge is maintaining this complexity without creating operational overhead that impacts development velocity and system reliability.
Compliance considerations add another layer of complexity. Different tenants might operate in different jurisdictions with varying data protection requirements. The authentication system must support these variations while maintaining a consistent validation approach across the platform. This might involve implementing compliance-specific validation paths or tenant-specific audit logging.
Scalability becomes a critical concern as the number of tenants grows. The authentication system must handle increasing load without degrading performance. Solutions include horizontal scaling of authentication services, tenant-aware caching strategies, and partitioning authentication data by tenant to ensure efficient access patterns.
Real-World Trade-offs and Case Studies
When implementing identity validation in microservices, real-world experiences reveal significant trade-offs that theoretical analysis might not capture. Organizations that have implemented these approaches consistently report that the optimal solution depends heavily on specific requirements, team expertise, and organizational context.
Let’s examine some common patterns from production environments. E-commerce platforms typically favor hybrid approaches, using local validation for standard browsing operations while requiring centralized validation for payment processing. This pattern balances performance needs with security requirements, but creates operational complexity in maintaining two validation systems. These platforms often report that the performance gains from local validation justify the additional complexity, especially during high-traffic events like sales.
Financial services institutions, conversely, tend toward centralized validation despite the performance implications. The regulatory requirements and security considerations in this sector demand consistent, auditable authentication across all services. These organizations implement sophisticated caching strategies and optimize authentication service performance to mitigate latency concerns. They report that the compliance benefits and security consistency outweigh the performance costs.
What about failure modes in production? Organizations using purely local validation report challenges with token revocation during security incidents. When a breach occurs, invalidating tokens across all services requires coordination between development teams and can delay response times. Those using centralized validation report better incident response capabilities but face availability challenges if the authentication service experiences issues.
Multi-tenant SaaS providers offer particularly interesting case studies. These organizations often implement tenant-aware hybrid approaches, with tenant-specific policies determining which validation method to use. For example, enterprise tenants might receive centralized validation for all operations, while small business tenants use local validation for most endpoints. This approach accommodates different risk profiles while maintaining operational efficiency.
Latency optimization in production reveals unexpected patterns. Many organizations find that the performance impact of authentication depends more on implementation details than the validation approach itself. Poorly optimized JWT validation, inefficient caching strategies, or network bottlenecks can negate the theoretical advantages of any approach. Organizations that invest in optimization often achieve excellent performance regardless of their validation strategy.
Operational overhead consistently emerges as a critical factor. Teams implementing complex validation systems report that maintenance, debugging, and evolving authentication requirements consume significant resources. Organizations with mature DevOps practices and dedicated security teams tend to manage this complexity better, while smaller organizations often struggle with the operational burden.
The most successful implementations share common characteristics: clear separation of concerns between authentication and business logic, comprehensive monitoring and alerting, and the ability to adapt authentication strategies as requirements evolve. These organizations treat identity validation as a first-class concern rather than an afterthought, investing in the infrastructure and expertise needed to implement robust solutions.
Best Practices for Identity Validation in Microservices
Implementing effective identity validation in microservices requires a strategic approach that balances security, performance, and operational complexity. Based on real-world experiences and architectural principles, several best practices have emerged that help organizations build robust authentication systems.
Start with a clear threat model that identifies authentication requirements based on risk assessment. Not all operations need the same level of authentication rigor. By categorizing operations by risk level, you can implement appropriate validation strategies – local validation for low-risk operations, centralized validation for high-risk operations, and potentially additional factors for the most sensitive operations. This targeted approach prevents over-engineering while ensuring adequate protection where it matters most.
Design your tokens carefully for both security and performance. JWT tokens should be as small as possible while containing all necessary information for authorization decisions. Include only essential claims that services need for access control, avoiding bloated tokens that impact performance. Consider implementing token compression techniques for environments with strict bandwidth constraints or high request volumes.
Implement comprehensive monitoring and alerting for authentication systems. Track metrics like validation latency, error rates, token validation failures, and revocation requests. Set up alerts for unusual authentication patterns that might indicate security incidents or performance issues. This visibility is crucial for maintaining system health and responding to security threats.
For multi-tenant platforms, implement tenant-aware authentication policies that can be configured per tenant. This flexibility allows you to accommodate different security requirements, compliance needs, and risk profiles while maintaining a consistent authentication infrastructure. Consider implementing tenant-specific authentication flows, session policies, and audit logging requirements.
Plan for failure scenarios before they occur. Implement circuit breakers, fallback authentication mechanisms, and graceful degradation strategies that allow the system to function even when authentication services experience issues. Document these failure modes thoroughly so teams understand how the system behaves during authentication service outages.
Invest in automation for operational aspects of identity validation. Automate key rotation, token revocation processes, and configuration management to reduce the risk of human error and ensure consistent implementation across services. Automation is particularly valuable in environments with many microservices or frequent deployments.
Maintain separation between authentication infrastructure and business logic. Authentication should be handled through well-defined interfaces that allow for implementation changes without affecting business code. This separation makes it easier to evolve authentication strategies, upgrade security components, and adapt to changing requirements.
Regularly review and update your authentication strategy based on emerging threats, new requirements, and operational experience. Authentication is not a one-time implementation but an ongoing process that requires continuous attention and improvement. Schedule periodic security reviews and architecture assessments to ensure your approach remains effective and aligned with organizational needs.
Sources
- AWS Microservices Documentation — Overview of microservices architecture principles and patterns: https://aws.amazon.com/microservices/
- JWT.io Token Validation Guide — Best practices for implementing JWT validation in distributed systems: https://jwt.io/introduction
- OWASP Authentication Cheat Sheet — Security guidelines for implementing authentication in microservices: https://cheatsheetseries.owasp.org/cheatsheets/Authentication_Cheat_Sheet.html
- Martin Fowler Microservices Resource — Comprehensive guide to microservices architecture and patterns: https://martinfowler.com/articles/microservices.html
- CNCF Security White Paper - Cloud native security best practices for distributed systems: https://github.com/cncf/tag-security/blob/main/whitepapers/README.md
Conclusion
Identity validation in microservices architecture represents a fundamental design choice with significant implications for system performance, security, and operational complexity. Local validation with short-lived contexts offers optimal performance and fault tolerance but introduces challenges with token revocation consistency. Centralized validation services provide perfect consistency and comprehensive security controls but introduce latency and create single points of failure.
Hybrid approaches emerge as the most practical solution for many organizations, allowing them to balance performance and security by applying different validation strategies based on risk level. For multi-tenant platforms, this approach becomes even more valuable, enabling tenant-specific authentication policies while maintaining system-wide performance.
The optimal solution depends heavily on specific requirements, risk profiles, and organizational context. Organizations should begin with clear threat models, implement comprehensive monitoring, and maintain separation between authentication infrastructure and business logic. Regardless of the chosen approach, continuous evaluation and improvement are essential as security threats evolve and organizational requirements change.
Ultimately, the best identity validation strategy in microservices is one that aligns with business objectives, accommodates operational constraints, and provides appropriate security for the specific risks involved. By understanding the trade-offs between different approaches and implementing them thoughtfully, organizations can build authentication systems that enhance both security and performance in their distributed architectures.
AWS defines microservices as an architectural and organizational approach where software is composed of small independent services that communicate over well-defined APIs. Each service can be developed, deployed, operated, and scaled independently, which is crucial for implementing effective identity validation strategies. The autonomous nature of microservices allows teams to implement different validation approaches based on specific security requirements and performance needs. This independence directly impacts how identity validation can be structured - either locally within each service or through centralized services. The specialized design of microservices means that identity validation can be tailored to specific business capabilities, potentially leading to more efficient and secure authentication mechanisms.